Your data security expert.
From static scans to dynamic data defense
Continuously map every data risk across your code, cloud, AI identities, and third-party ecosystem — with full context already assembled.
Traditional DSPM misses data that exposes you
Traditional DSPM tools scan data at rest and report what they find. In a world where data instructs AI and flows across code, cloud, SaaS, and third parties at machine speed, static scanning creates a false sense of security.
Data velocity outpaces discovery
- Traditional DSPM only sees a fraction of actual data flows because it scans storage, not motion
- Critical sensitive data is hidden in source code, runtime environments, CI/CD pipelines, and AI training data
- Manual discovery cannot keep pace with data velocity across modern enterprise architectures
Blind spots between data and AI
- Static scans miss dynamic data transformations, API calls, and AI model interactions
- Data flowing into and out of AI agents, models, and MCP servers is invisible to traditional DSPM
- Fragmented tools create gaps between data security, AI security, and privacy teams
Discovery without context is just inventory
- Scanners tell you what data exists and where it sits. They cannot tell you the story of your data—what it’s doing, who’s accessing it, or why.
- Alerts without business context can’t be prioritized or triaged.
- Without business purpose and legal obligations mapped to each flow, remediation is guesswork.
From DSPM to AI data defense
Traditional DSPM tools deliver periodic snapshots of data at rest. Relyance AI shows how data moves, who can reach it, and where it is exposed - continuously and with full context.
Everything that can reach your data — mapped continuously
Ditch periodic scans that miss data in motion. Relyance AI follows sensitive data from source code to cloud to AI — surfacing risks as they emerge.
Real-time data inventory — across data at rest, data flows, and AI assets
Unified blast radius view — by PII type, asset count, and flow destination
Code-to-cloud coverage — including MCP servers, AI agents, and third-party vendors
Every flow arrives with the full context-chain already assembled
Not "customer data is flowing through Salesforce." Instead: data type, data subject, cross-border paths, and protection state — surfaced automatically for every finding, without manual reconstruction.
Powered by Data Journeys™ — connecting data, identity, and infrastructure
Cross-border and protection state — visible per finding, per flow
Business and operational impact — understood instantly, not reconstructed manually
From risk identified to risk resolved — in seconds, not weeks
Reduce false positives and eliminate the investigation tax. A unified policy view across data, identity, and AI posture — with severity and context already assembled — lets Lyo™ answer "What is the blast radius of this AI agent's access?" in seconds.
Unified policy violations view — across data, identity, and AI posture
Ask Lyo™ in natural language — get a definitive answer with full context
Code-level remediation — find the exact commit and know what to do
Real-time data flow intelligence across code, cloud, and AI
Trace every flow from code to cloud to AI model in real time. The Data Exposure Graph connects data sensitivity, identity permissions, and AI agent behavior to surface compound risks that only emerge at the intersection. Unified obligations mapping ties every flow to its legal, contractual, and policy requirements automatically.

How does Relyance AI secure enterprise data?
Relyance AI secures enterprise data through four layers. First, it discovers and classifies sensitive data across code, cloud runtime, data stores, SaaS applications, AI systems, and third parties in real time, not through periodic scans. Second, it maps identity-to-data relationships for both human and non-human identities like service accounts and AI agents to surface compound risks and overprivileged access. Third, it monitors continuously with 24/7 policy-based alerting and recommends contextual remediation that explains why a risk exists and how to fix it. Fourth, it monitors policy-aware guardrails at machine speed to prevent incidents before they occur. The platform is agentless, API-first, and powered by Lyo™, the world's first autonomous data defense engineer.
Relyance AI vs. traditional DSPM tools
Traditional DSPM tools scan data at rest and report findings for humans to investigate. Relyance AI traces data in motion, correlates data with identity and behavior, delivers contextual remediation recommendations, and monitors guardrails continuously. DSPM is a core capability within the Relyance AI platform, not a standalone product. Discovery is the starting point, not the destination.



Traditional DSPM scans static data. Relyance AI tracks complete data lifecycle intelligence.
Watch: Track fast-moving sensitive data
What security leaders say
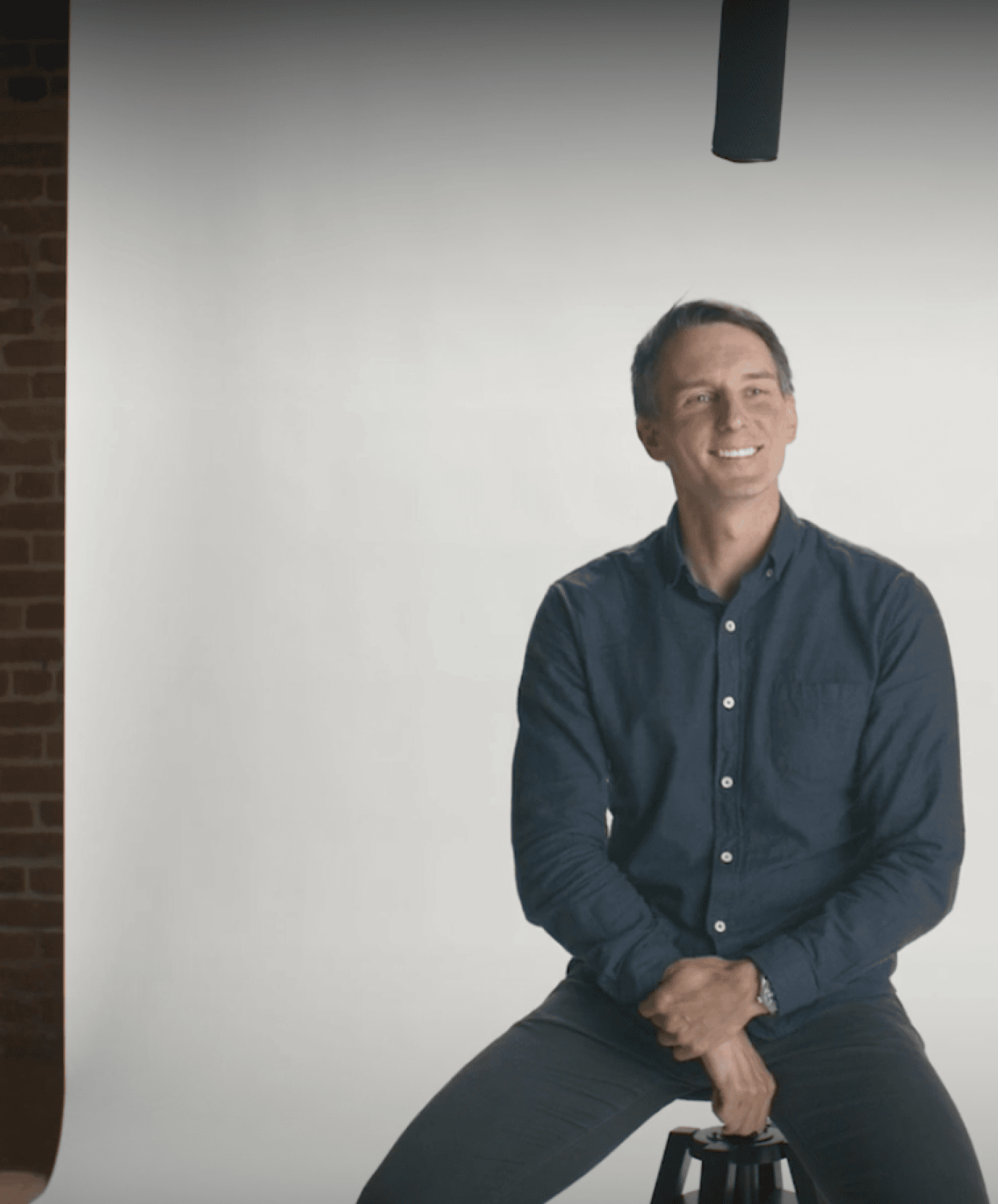

“AI is creating and moving data faster than any team can track. Only AI-native tools like Relyance AI can keep up with the discovery and enforcement loop.”
Chris Bender, CISO
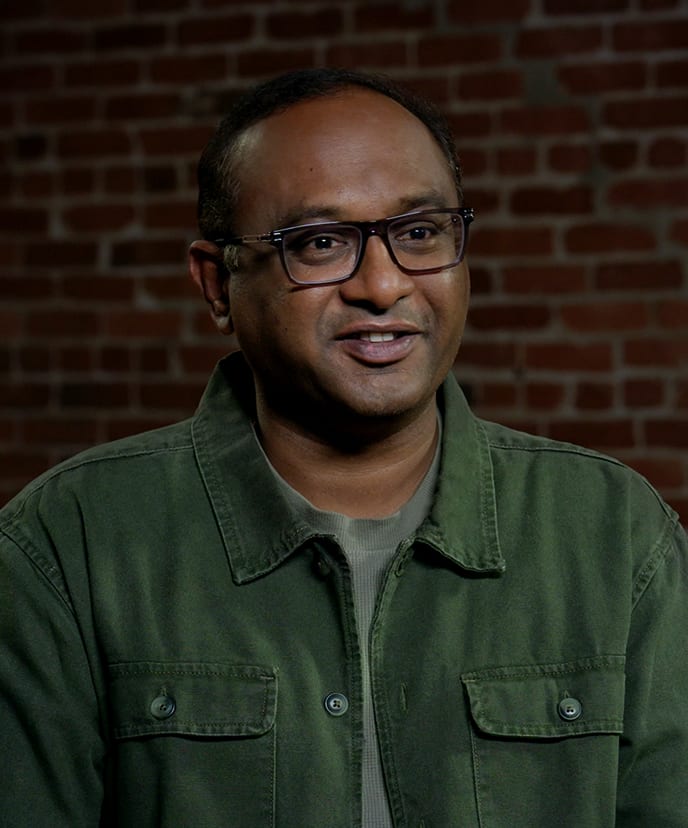

"Most tools show me a snapshot. Lyo™ gives me the full movie, around the clock. I can't afford to choose between innovation and security."
Karthik Chakkarapani, SVP & CIO


“Relyance gives us a complete, contextual understanding of our data landscape. We can see what we have, how it's used, who owns it, and where the risks are. This level of clarity is strengthening our overall security posture."
Jason James, CIO
FAQ
What is data security posture management (DSPM)?
DSPM is the practice of discovering, classifying, and monitoring sensitive data across an organization's cloud, SaaS, and on-premise environments to identify security risks and compliance gaps. Traditional DSPM tools scan data at rest to answer the question "what sensitive data do we have and where is it?" This foundational visibility is essential, but in today's AI-driven enterprise, it is the starting point for data security, not the destination.
What is dynamic DSPM and how is it different from traditional DSPM?
Dynamic DSPM traces data in motion rather than scanning data at rest. Traditional DSPM takes periodic snapshots of your data landscape. Dynamic DSPM continuously maps how data flows across code, cloud, SaaS, third parties, and AI systems in real time, capturing every transformation, API call, and model interaction. This means you see not just what data exists, but what it's doing, where it's going, who or what is accessing it, and why. Relyance AI pioneered this approach through its proprietary Data Journeys technology.
Why isn't traditional DSPM enough for the AI era?
Traditional DSPM was designed for a world where data sat in databases and applications were deterministic. In the AI era, data instructs software, AI agents access and transform data autonomously, and data flows across code, cloud, SaaS, MCP servers, and third parties at speeds no periodic scan can track. Traditional DSPM misses data in code repositories and CI/CD pipelines, runtime data transformations, data flowing into and out of AI models and agents, and the identity relationships between AI agents and sensitive data. These are the exact blind spots where the most dangerous risks live.
What is the difference between DSPM and AI-SPM?
DSPM focuses on securing an organization's data assets: discovering, classifying, and monitoring sensitive data across environments. AI-SPM focuses on securing AI assets: discovering AI models, agents, tools, and monitoring their security posture. In practice, the two are deeply connected because AI risk depends entirely on what data AI systems can access. Tools that separate DSPM from AI-SPM create the blind spots they claim to eliminate. Relyance AI unifies both as capabilities within a single data defense platform, so you see the full picture of how AI and data interact.
What is compound risk in data security?
Compound risk is a security vulnerability that forms when individually low-risk elements combine to create a critical threat. For example, an AI agent alone may not be dangerous. A database with customer PII may be properly secured. But an AI agent with administrative access to that database creates a lethal combination that no individual scan would flag. Compound risks are invisible to tools that assess data posture and identity posture separately. Relyance AI detects compound risks by correlating data sensitivity, identity permissions, and access behavior in real time.
How is Relyance AI different from other DSPM vendors like Wiz, Palo Alto, or Cyera?
Most DSPM vendors discover and classify sensitive data in cloud storage and databases — but stop there. They don't follow data as it moves, track how AI systems access it, or connect it back to the source code where risk originates. Relyance AI takes a data-first approach—starting from the data journey itself and tracing how data flows from code to cloud to AI model to third party. This means Relyance discovers sensitive data in places other DSPM tools miss: source code, CI/CD pipelines, runtime transformations, and AI training and inference flows. Relyance also maps identity-to-data relationships for both human and non-human identities, delivers contextual remediation (not just alerts), and unifies data security with AI security and privacy in a single platform.
What is identity-to-data intelligence?
Identity-to-data intelligence maps how human users, service accounts, AI agents, and automated workflows gain access to sensitive data. It traces permission chains across your environment to identify overprivileged access, dormant permissions, and risky combinations of identity and data sensitivity. In the age of agentic AI, non-human identities (AI agents, MCP servers, automated pipelines) often outnumber human users and carry significant access privileges. Identity-to-data intelligence makes these invisible relationships visible.
How does Relyance AI manage data flowing through AI systems?
Relyance AI discovers and classifies data across AI models, AI agents, MCP servers, and third-party AI tools alongside traditional data stores, cloud services, and SaaS applications. The platform traces how data enters AI training pipelines, how AI agents access sensitive data at runtime, and how data flows between AI systems and other enterprise assets. This unified view across AI and non-AI data assets is what enables compound risk detection.
What compliance frameworks does the data security expert support?
Relyance AI maps data flows and security posture to obligations under GDPR, CCPA/CPRA, HIPAA, SOX, PCI DSS, NIST CSF, ISO 27001, and sector-specific regulations. The platform continuously detects potential compliance gaps and generates audit-ready evidence in seconds, with every data flow linked to its relevant legal, contractual, and policy obligations.
Does Relyance AI require agents to deploy?
No. Relyance AI is fully agentless and API-first, designed for petabyte-scale enterprise environments. Deployment options include full SaaS (managed cloud for rapid deployment), InHost (runs entirely within your VPC), and DirectConnect (private link between your network and the platform).
Who is the data security expert built for?
The data security expert is built for CISOs, security engineering teams, data engineering teams, and compliance leads at mid-size and enterprise organizations. It is designed for companies with complex data ecosystems spanning cloud, SaaS, code repositories, and AI systems that need unified visibility into where sensitive data lives, how it moves, who or what accesses it, and whether it complies with policy.
You may also like

Privacy in the trenches: What we learned (and what we laughed about) at IAPP Global Summit

RSAC™ 2026 Conference recap: Securing AI starts with understanding your data