A single view of exposures and their impact
Stop juggling disconnected tools. Relyance AI unifies Data Posture, AI Security, Identity, Third Party, Data Residency & Sovereignty, and Privacy risk into a single live dashboard — so you understand your risk exposure and the business impact at a glance.
Risk is fragmented across your security stack
Security teams manage risk across six or more categories using tools that were never designed to talk to each other. The result: compounding threats that span data, identity, and AI go undetected because no single tool sees the full picture.

No unified view of cross-domain risk
Data posture, identity posture, AI posture, privacy, third-party risk, and data residency are tracked in separate tools with separate policy models. Security leaders piece together risk exposure manually, if at all.

Compounding threats invisible across silos
A data residency violation alone may be low severity. An overprivileged AI agent alone may be medium. But when that agent accesses cross-border PII through an unreviewed third party, the combination is critical. Siloed tools score each finding independently and miss the compound exposure.

Remediation slowed by tool fragmentation
When a finding spans data, identity, and AI, your team investigates across four or more dashboards before understanding severity, scope, or what to do. That investigation tax turns hours into days, increasing time to resolution.
From signals to answers. The full risk picture, always on.
Traditional tools show you risk in fragments. Relyance AI correlates findings across data, identity, AI, privacy, third-party, and sovereignty risk into one live view with one policy model, so you understand exposure and impact without stitching tools together.
One unified view across six risk vectors.
Monitor Data Posture, Identity Posture, AI Posture, Data Residency & Sovereignty, Privacy, and Third Party risk across a single interface and policy model — with prioritized findings surfaced automatically.
Single unified view — monitor risk across multiple categories in one view against one policy model, not fragmented across six separate tools
Prioritized findings — risks ranked by severity and business impact across every category
Always on — continuous monitoring, not periodic scans
Identify compounding risk to minimize your exposure.
Secure risks across your data estate, including AI and non-AI assets, with the context to understand their behavior and limit their blast radius. Drill into findings to understand the full context and downstream impact.
Compound risk detection — understand how combined risks across categories create critical exposure
Single policy model— define and track multiple risk dimensions across AI and non-AI assets in one place, against a single automated policy model
Drill-down detail — click into any finding for full context on impacted assets, identities, and obligations
Know exactly what to fix and how.
Filter policy violation findings by category, severity, or asset for contextual remediation recommendations on every single issue — so your team acts with confidence, not guesswork.
Filtered issue view — quickly surface the findings that matter most
Remediation recommendations — step-by-step guidance - for example, how to encrypt data elements and enforce least privilege
Governance context — every finding shows impacted obligations and controls alongside the fix
Real-time data flow intelligence across code, cloud, and AI
Trace every flow from code to cloud to AI model in real time. The Data Exposure Graph connects data sensitivity, identity permissions, and AI agent behavior to surface compound risks that only emerge at the intersection. Unified obligations mapping ties every flow to its legal, contractual, and policy requirements automatically.

How does Relyance AI secure AI systems?
Relyance AI manages unified risk through three layers. First, it aggregates findings across six risk categories into a single interface with a single automated policy model, so security teams monitor Data Posture, Identity Posture, AI Posture, Data Residency and Sovereignty, Privacy, and Third Party risk in one view. Second, it correlates findings across categories to surface compound risks that siloed tools miss, attaching the full context chain to every violation: what is wrong, why it matters, which assets and identities are involved, and what obligations are impacted. Third, it delivers contextual remediation recommendations on every finding with governance context included, so teams know exactly what to fix, how to fix it, and which controls and obligations are at stake.
The platform is agentless, API-first, and powered by Lyo™, the world's first AI-native data defense engineer.
Relyance AI vs. fragmented risk tools
Traditional security stacks require separate tools for data security, identity, AI security, privacy, and third-party risk. Each tool has its own policy model, its own severity scoring, and its own remediation workflow. Findings that span categories require manual correlation across dashboards. Relyance AI replaces this fragmented approach with a single risk view and a single policy model. Compounding risks are surfaced automatically. Context and remediation are assembled for every finding. Unified risk is core to the Relyance AI platform, not a separate dashboard bolted on.



Most security teams manage risk across six or more disconnected tools.
What security leaders say
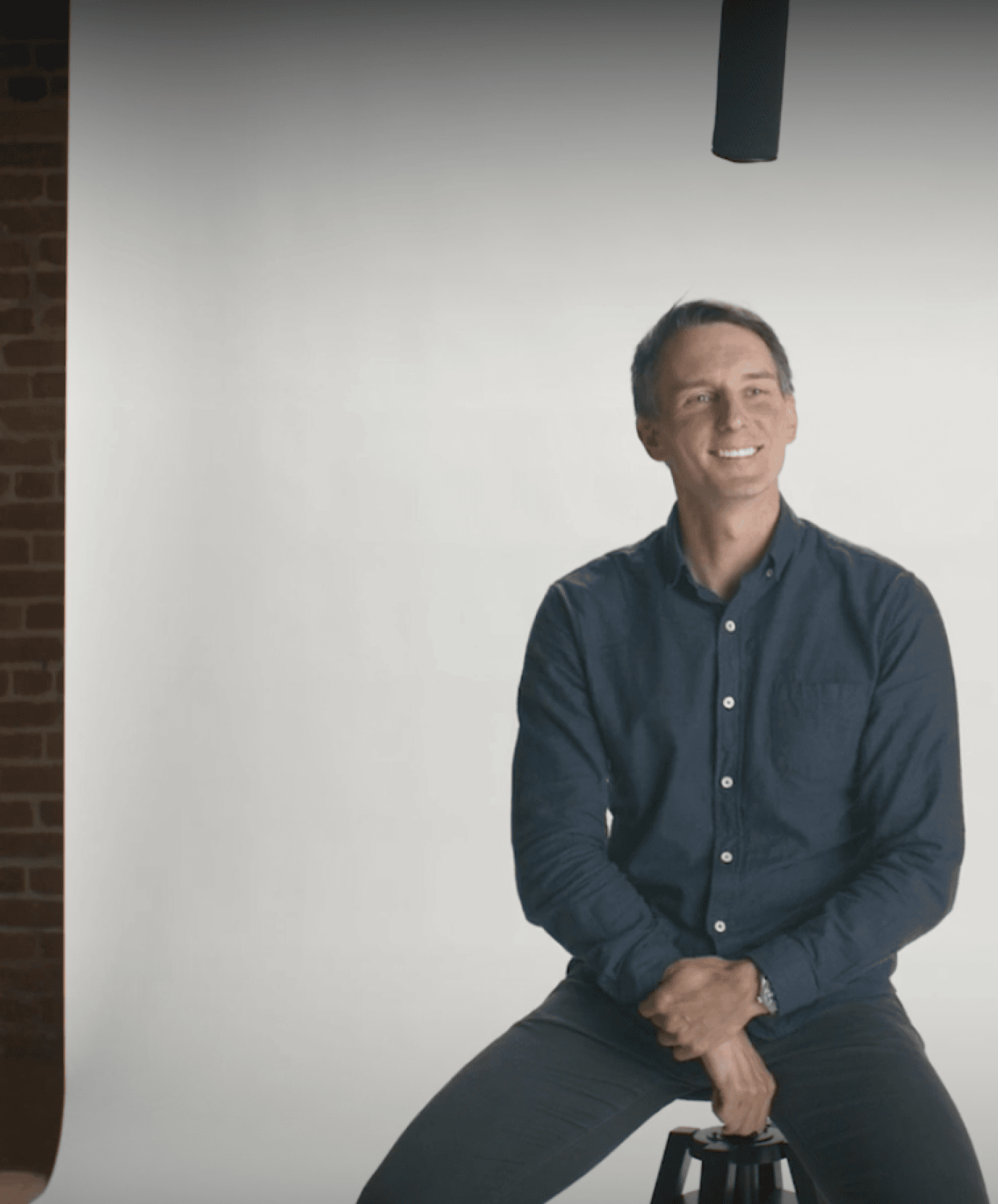

“AI is creating and moving data faster than any team can track. Only AI-native tools like Relyance AI can keep up with the discovery and enforcement loop.”
Chris Bender, CISO
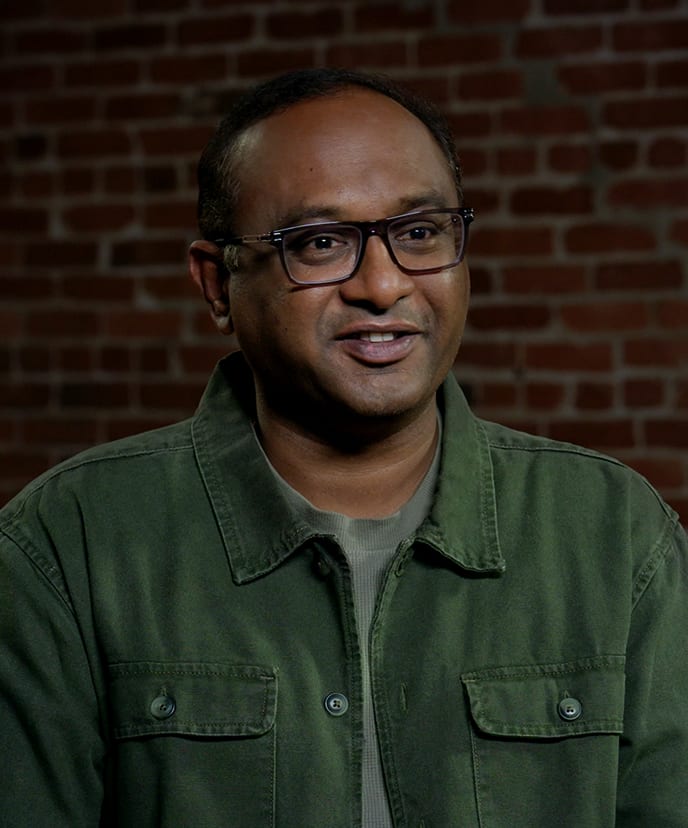

"Most tools show me a snapshot. Lyo™ gives me the full movie, around the clock. I can't afford to choose between innovation and security."
Karthik Chakkarapani, SVP & CIO


“Relyance gives us a complete, contextual understanding of our data landscape. We can see what we have, how it's used, who owns it, and where the risks are. This level of clarity is strengthening our overall security posture."
Jason James, CIO
FAQ
What is Unified Risk management in data security?
Unified risk management is the practice of monitoring, correlating, and remediating security findings across multiple risk categories in a single platform with a single policy model. Instead of managing data posture, identity posture, AI posture, privacy, third-party risk, and data residency in separate tools, unified risk brings all six dimensions into one view so that compound risks that span categories are detected and resolved together.
Why do siloed security tools miss compounding risk?
Siloed tools assess findings within their own category. A data posture tool scores a sensitive data exposure independently. An identity tool scores an overprivileged access finding independently. Neither tool sees that the two findings are connected and together create a critical compound threat. Compounding risk only becomes visible when data, identity, and AI behavior are correlated in real time within a single platform.
What risk categories does unified risk cover?
Relyance AI's unified risk view covers six categories: Data Posture, Identity Posture, AI Posture, Data Residency and Sovereignty, Privacy, and Third Party risk. All six are monitored continuously against a single automated policy model with prioritized findings and contextual remediation.
How is unified risk different from a SIEM or security dashboard?
A SIEM aggregates alerts from multiple sources into one interface, but findings are still scored and investigated independently. Unified risk in Relyance AI correlates findings across categories, surfaces compound risks automatically, and delivers contextual remediation with full governance context on every finding. It is not alert aggregation. It is risk correlation with action.
How does Relyance AI prioritize findings across risk categories?
Every finding is scored by severity and business impact using a single policy model that spans all six risk categories. Compound risks that emerge at the intersection of multiple categories are automatically elevated. Each finding includes the full context chain: impacted assets, identities, obligations, and controls, so teams can prioritize and act without manual investigation.
Does unified risk with Relyance AI require deploying additional agents or tools?
No. Unified risk is a core capability within the Relyance AI platform. It requires no additional agents, sensors, or integrations beyond the standard agentless, API-first deployment. All six risk categories are monitored from the same platform with the same deployment.
Who is unified risk built for?
Unified risk is built for CISOs, security operations teams, and compliance leads at organizations that need a single view of risk exposure across data, identity, AI, privacy, third-party, and sovereignty categories. It is designed for teams that are currently managing these categories across multiple tools and need to consolidate into one platform with one policy model.
You may also like

Privacy in the trenches: What we learned (and what we laughed about) at IAPP Global Summit

RSAC™ 2026 Conference recap: Securing AI starts with understanding your data